OBJECTIVES
The goal of the course is to prepare professionals for the challenging CISSP examination by covering the syllabus defined in the (ISC) 2 common body of knowledge.
BONUS TAKE AWAY ON "CYBER SECURITY E-COURSE
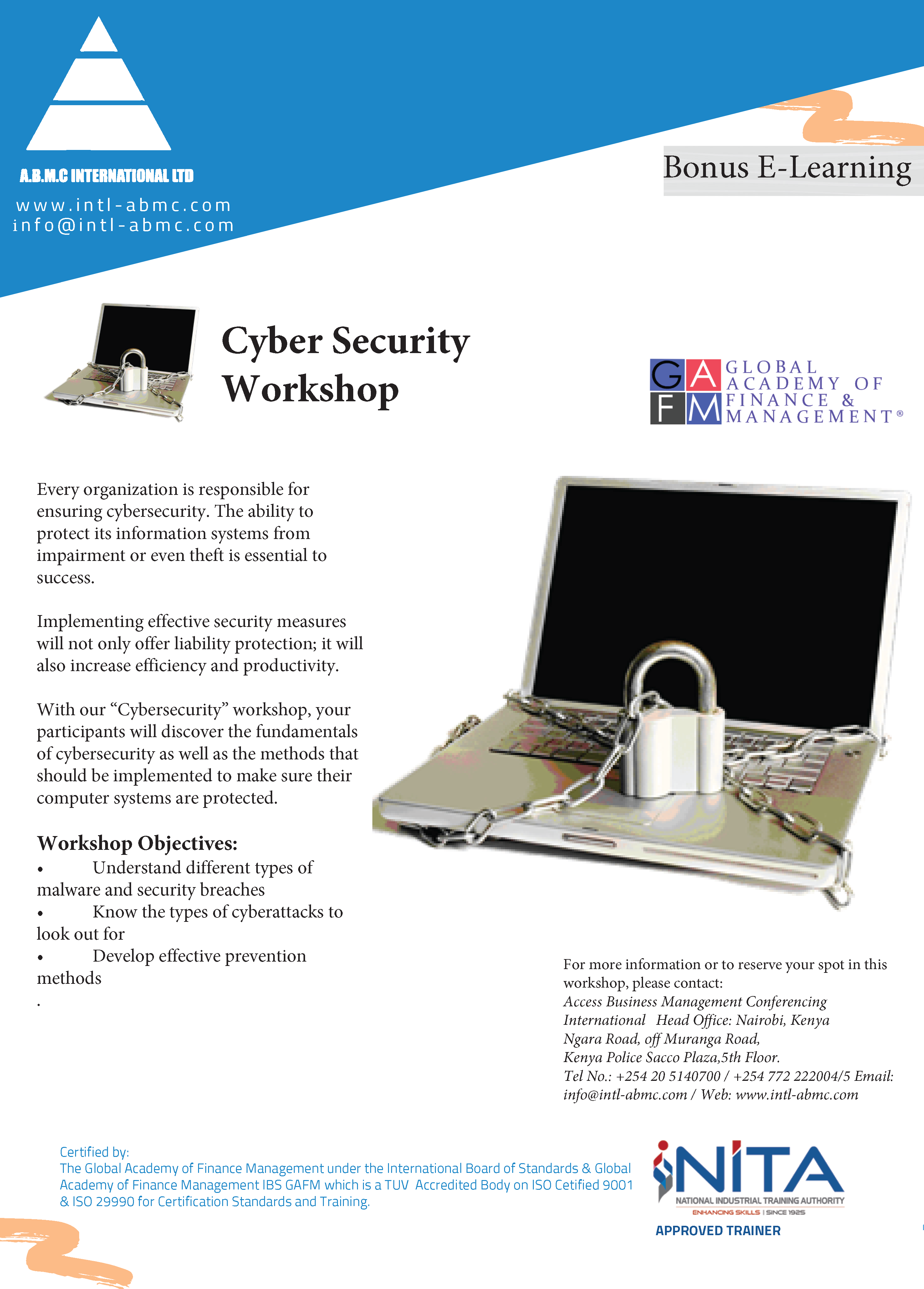
E-COURSE
E-COURSE
TRAINING IS PROVIDED BY ABMC INTERNATIONAL LTD
OUR TRAINING PROGRAMS ARE ACCREDITED AND SUPPORTED BY LEADING HR INSTITUTIONS LISTED BELOW
ABMC INTERNATIONAL
P.O Box 52303 - 00100, Nairobi, Kenya
ABMC INTERNATIONAL © 2020
All rights reserved.